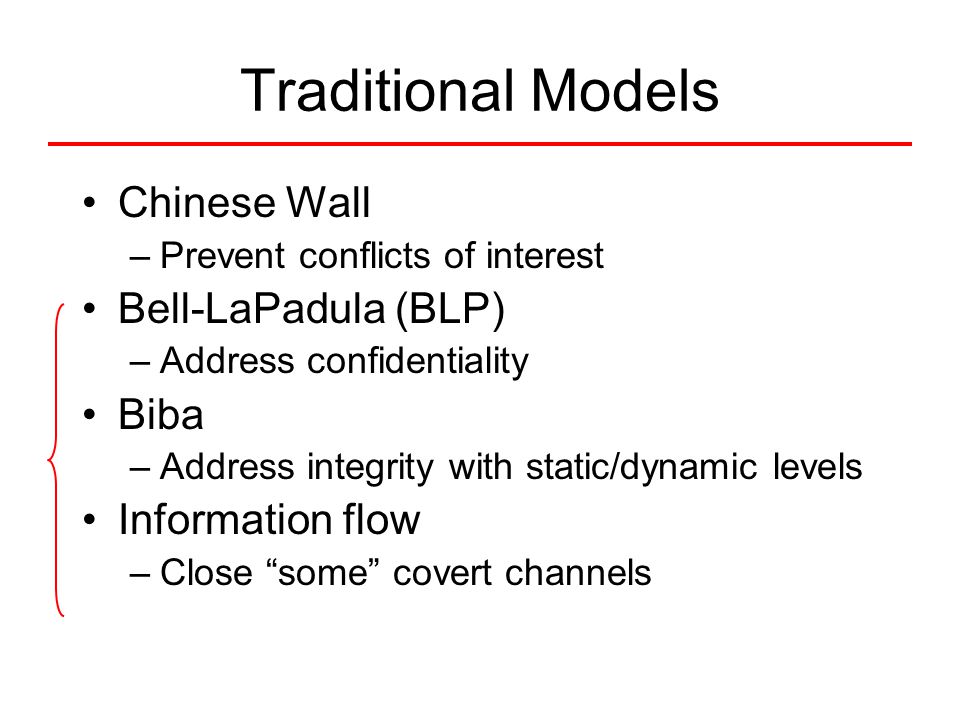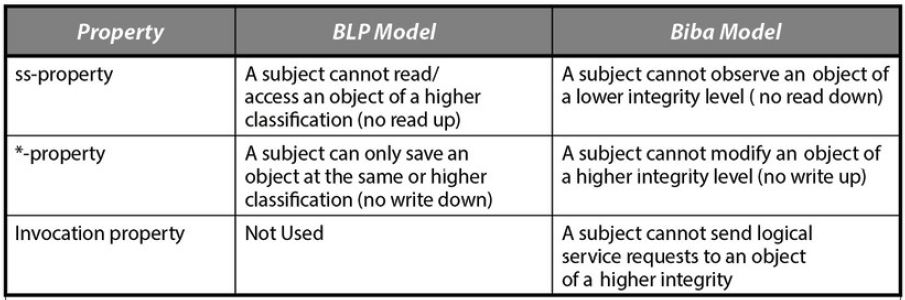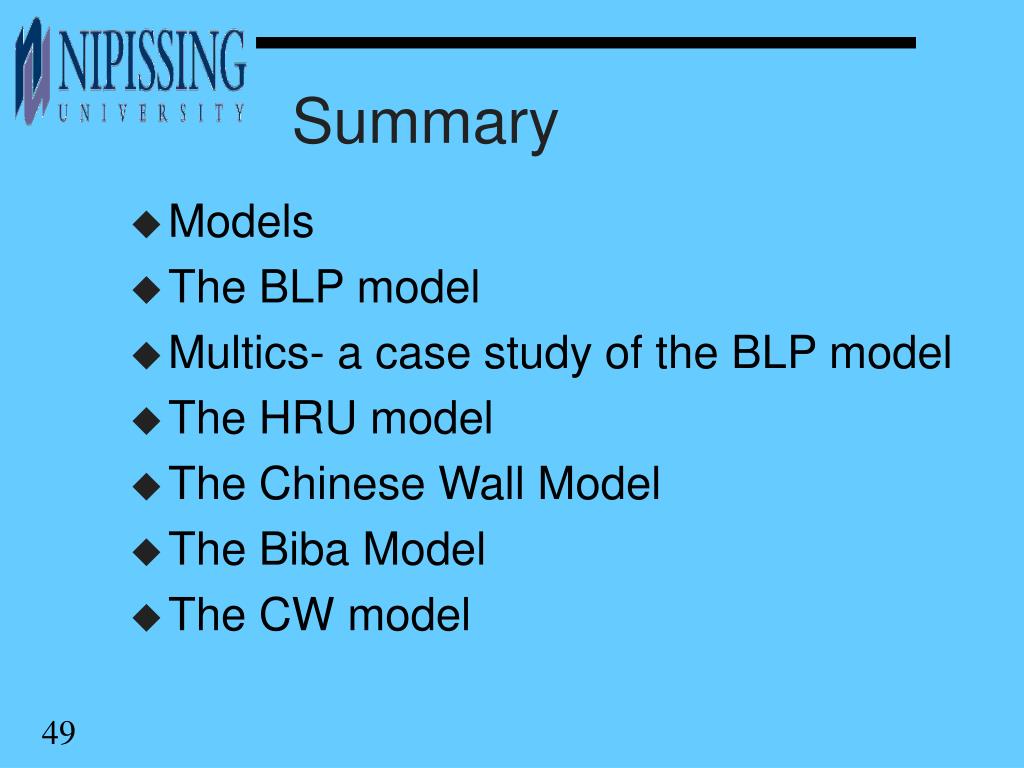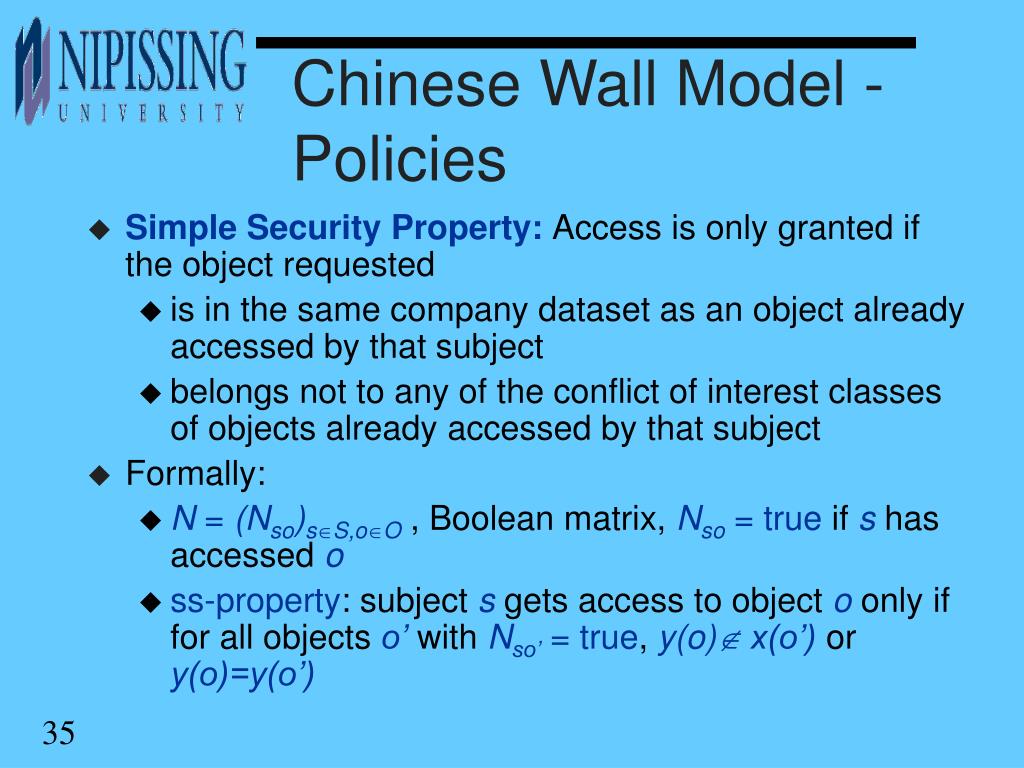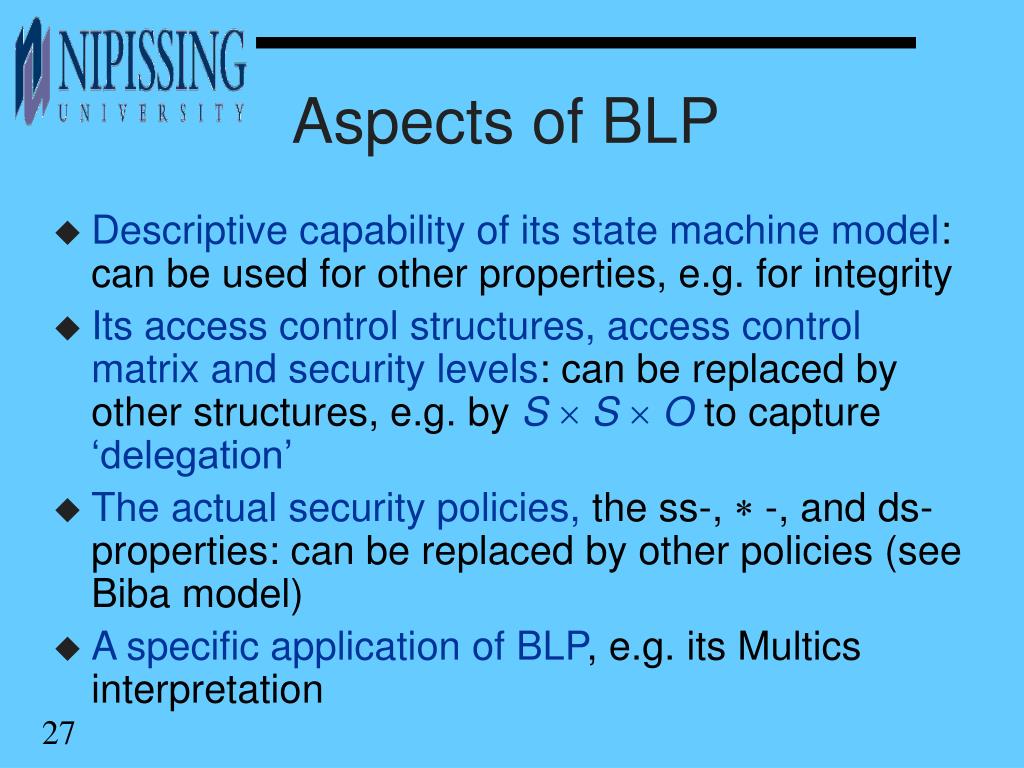
1 Lecture 3 Security Model. 2 Why Security Models? u A security model is a formal description of a security policy u Models are used in high assurance. - ppt download

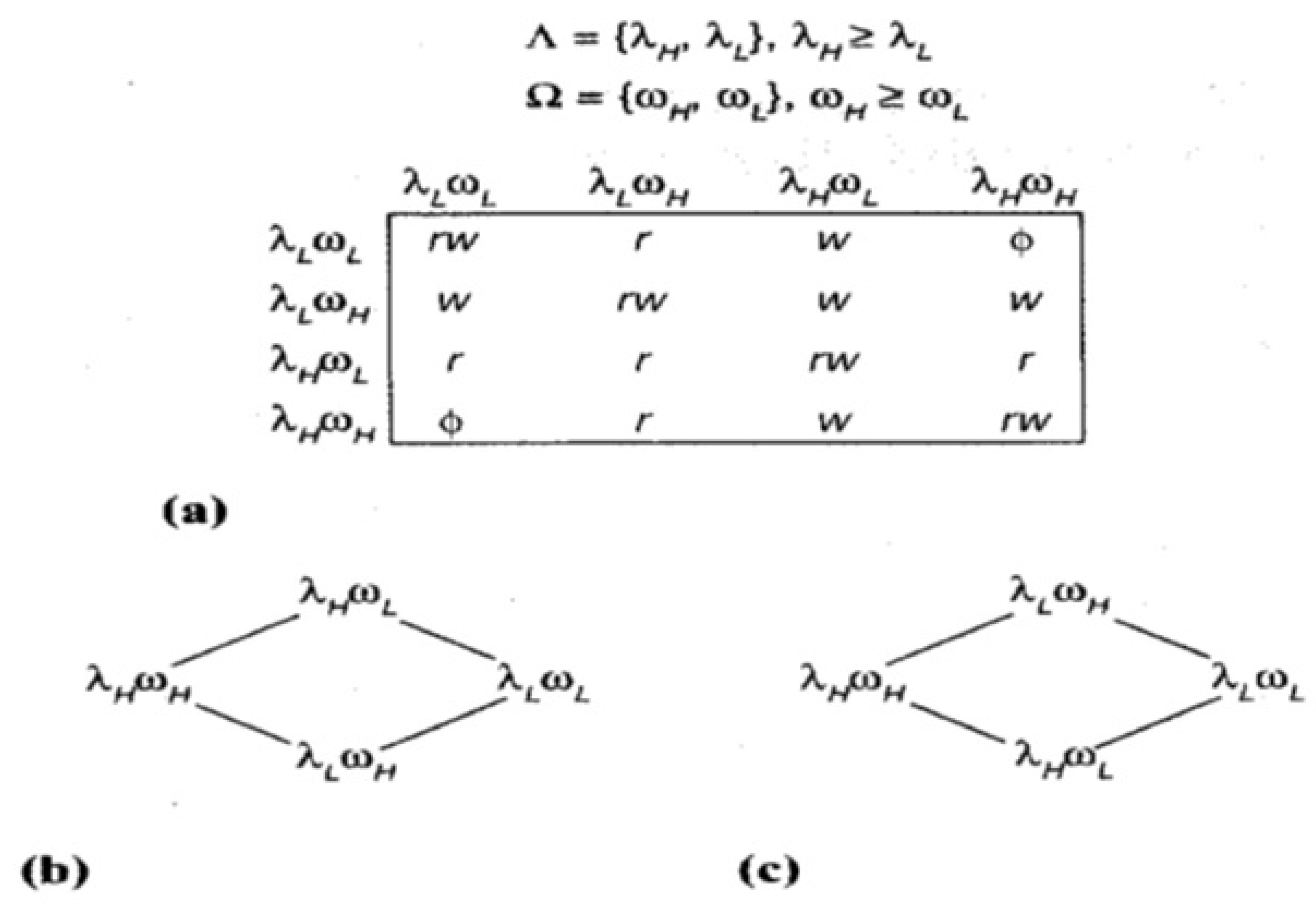
Generic metamodels for expressing configurations of (a) DAC; (b) BLP... | Download Scientific Diagram

Generic metamodels for expressing configurations of (a) DAC; (b) BLP... | Download Scientific Diagram